Why Email Security is a Top Cyber Security Control

Cyber security frameworks play an integral role in ensuring organisations have adopted the latest and best practice standards and strategies to safeguard their information systems and data. The most commonly adopted industry standard frameworks include the NIST Cyber security Framework, the CIS Controls, and ISO/IEC 27001/2. But, of these industry frameworks, only the ISO/IEC 27001/2 standard […]
Cyber Security: Protect What You Have
There is a saying often used when discussing the route to happiness: “Want what you have.†Its origins aren’t entirely clear. I’d originally thought it to be something profound from a Buddhist movement, but Google seems to suggest an author or other famous folk. Essentially, what it means is: if you want what you have […]
AI in Cyber Security Part 1: Infiltration Into the Market
With ChatGPT capturing the attention of the global stage, dinner discussions and boardroom breakdowns alike are pondering the next ‘big thing’. Concern over generative AI is even creating widespread unease in the Hollywood writers’ scene. In 2023, AI and ML (machine learning) are ubiquitous. We make artwork with it; we use it in ‘human-style’ chatbots […]
AI in Cyber Security Part 2: Reinventing Corporate Defences
In Part 1 of this article we explored how AI is infiltrating the cyber security landscape. Today we dive deep into the AI abyss to demonstrate how new AI and machine learning (ML) technologies are reinventing the way in which organisations across the world think about — and react to — new cyber threats. The […]
What Have We Learned from GDPR?
A blog from guest author Trinny Truu, Field Marketing Manager at Cleo. It’s been almost 12 months since businesses all over started panicking about the European Union’s General Data Protection Regulation (GDPR) and with the one-year anniversary fast approaching (25 May 2019), what have we learned over this past year? The introduction of GDPR made […]
Cloud still requires some blue sky thinking
A guest blog from James Phillips, Senior Marketing Manager at Titus In the conversations I have with customers around the world, it’s clear that when it comes to data, one of the biggest challenges is being able to see where it is located. Without that critical insight, it becomes exceedingly difficult to control where data […]
How Security Professionals can Solve the Biological need to Break the Rules
A blog from guest author, Dave Barnett, CASB Specialist at Forcepoint Would you allow someone else to delete the apps on your phone? Like many, I have an emotional connection with my device and what’s on it, so woe betide anyone touching my apps. However, I use my device for both work and personal activities, […]
Managed File Transfer Predictions 2021
Like most people I’ll be happy to see the back of 2020, it’s been a tough year for all and sundry. Without beating the COVID-19 drum too much, it is easy to see how its shaped our lives in more ways than one. One such way is undoubtedly the major shift to different working patterns […]
MFT, SWIFT, and the Fight Against Cyberfraud
As businesses across the world continue to expand globally, the volume of global payment transfers is growing along with them. The world’s largest electronic payment message system, SWIFT, saw a 5.4% YoY increase in message transfers as of May 2019. SWIFT, or The Society for the Worldwide Interbank Financial Telecommunication, is a network that enables over 11,000 […]
Deloitte Data Breach: What Were They Thinking?
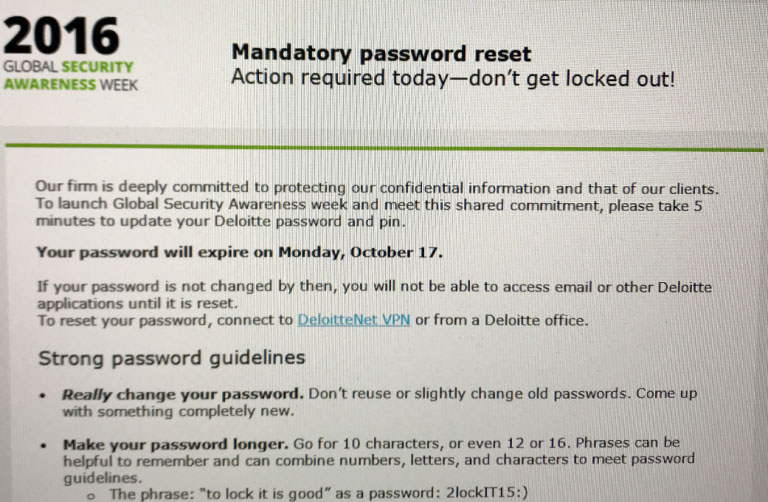
Let me make this clear right from the off, this isn’t another blog merely hammering an organisation that has had the misfortune to suffer a breach, that would be as churlish as it is stupid. The reality is a breach could probably occur to almost anyone and taking delight in the failure of a company […]