Have you seen the mail I just sent?
In 1971 the first ever One Day International cricket match was played; the Nasdaq stock exchange was founded, and Led Zeppelin first played Stairway To Heaven. It was also the year the first electronic mail was formalised in the Request For Comment (RFC) 196 through what became known as the Mailbox Protocol. Ironically, this protocol […]
Axiomatics and HANDD Business Solutions Partner to Deliver Dynamic Authorization
Axiomatics, the leader in delivering award-winning, next-generation authorization, today announced a reseller partnership with HANDD Business Solutions (HANDD), a UK-based independent specialist in global security. The partnership extends Axiomatics’ Orchestrated Authorization strategy to reach HANDD’s customer base across 27 countries worldwide. Axiomatics’ award-winning attribute-based access control (ABAC) enables organizations to ensure access decisions are made in real-time. Leveraging this platform, […]
The Reason Your Cloud Platform Needs Policing
According to recently published data from the UK based ISP Zen Internet, up to 89% of technology is soon to be hosted “off-premiseâ€. For anyone who’s not lived in a cave for the past few years this is hardly surprising. Cloud operations suited so much of our business needs and wants pre-2020, but without a […]
Policing in the Shadows, from home!
2020 – 2021 was a dream year for cloud computing and the hyperscalers; their profit margins describe that in a far better way than I ever will. So much so that I’m sick of talking about working from home, not working from home, the inevitable small talk when you meet the in-laws… “Are you back […]
The outlook is cloudy: The importance of Data Classification and Data Access Governance tools
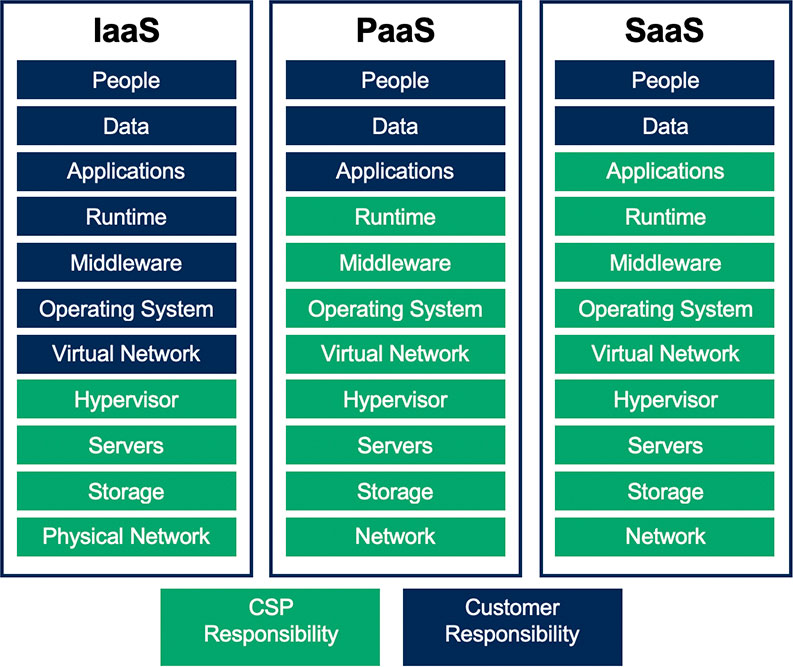
By the end of the year 2020 it is predicted that 60% of organisations will use an external service provider’s cloud managed service offering. That is double the amount doing so two years ago. With cloud adoption not slowing down and even accelerating as a result of the Covid-19 pandemic, organisations can be forgiven for […]
Deloitte Data Breach: What Were They Thinking?
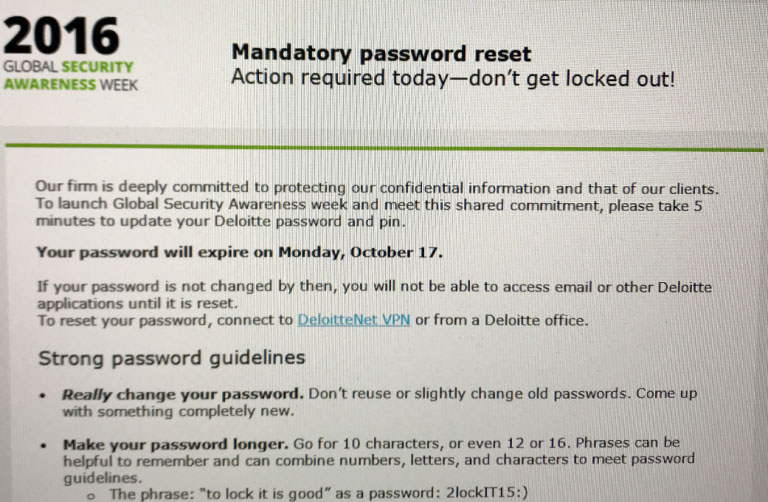
Let me make this clear right from the off, this isn’t another blog merely hammering an organisation that has had the misfortune to suffer a breach, that would be as churlish as it is stupid. The reality is a breach could probably occur to almost anyone and taking delight in the failure of a company […]
UEBA: Artificial Intelligence Just Got Intelligent
There is a real buzz in the industry around artificial intelligence, machine learning, automated network monitoring and user & entity behaviour analytics (UEBA) at the moment. Artificial intelligence (AI) is hardly a new concept, but part of the norm with any mention of anything AI related, it’s hard not to be afraid or fearful of […]
Responding to a Data Breach – A Five-Step Guide
With high profile breach hitting the headlines on an almost daily basis (or so it seems) the chances of suffering a breach are not so much if but when. The average cost of a breach has now reached $4 million according to recent research conducted by the Ponemon Institute and so should the worse happen […]
5 Key Use Cases for User & Entity Behaviour Analytics
Last year, Gartner suggested the average time taken to detect a cyber attack, was an astonishing 205 days. The potential damage that could be done in the that time frame is alarming to say the least. This kind of research has drawn a great deal of attention to the need for enterprises to put in […]
Why Data Classification Should be Central to Every Organisation’s Security Strategy
In 2016 internet traffic surpassed the one zettabyte point that’s according to Samsung which equates to one billion terabytes worth of data, or 1 trillion gigabytes. In short that’s a lot of data and it’s a figure that will keep on growing. Data is at the heart of every business which is why data classification […]