HANDD are named as a supplier on G-Cloud 14
HANDD Business Solutions (HANDD) is thrilled to announce that we have been named as a supplier on Crown Commercial Service’s (CCS) G-Cloud 14 framework on the following Lots: Lot 2: Cloud Software Lot 3: Cloud Support CCS supports the public sector to achieve maximum commercial value when procuring common goods and services. In 2022/23, CCS […]
The Ultimate Guide to Data Loss Prevention

What is DLP? Decades of digital technology transformation have given employees amazing powers. But with that power also comes the ability to send millions of dollars in just a few clicks, or share an entire customer database in a single emailed file. Today, your people are often the gatekeepers to your company’s most sensitive systems […]
Five Steps To A Secure Workforce

Companies thrive on talent. Your employees are the key to success in business, especially when you use technology to make them more productive. This access to data and applications can also pose dangers, though. An employee using data inappropriately – either maliciously or unwittingly – can incur reputational, legal and financial risk for your business. […]
60 Second Interview With Danny Maher
Welcome to June’s 60 Second Interview. Here you can find out all you need to know about the Pre-Sales and Professional Services function at HANDD Business Solutions from one of the industry’s most impressive Pre-sales Managers, Danny Maher. We asked him… Q: What does it say on your business card? Danny Maher, Pre-Sales Manager at […]
Insider Threat: Why Trusted Access Can Be Your Biggest Data Vulnerability
While much attention is given to external cyber threats, insider threats pose an equally significant risk to any organisation’s data. The systems and identities which make up your organisation interact with the data you hold daily to perform their jobs. This naturally gives them a much larger attack surface, risk profile and remit for malicious […]
Securing Your Supply Chain: Managing Third-Party Risks to Safeguard Data
Third-party and supply chain risks are significant for data security and protection as they extend the risk landscape beyond the organisation’s direct control and address space. This requires stringent oversight, rigorous assessment, and continuous monitoring of third-party practices to safeguard sensitive data and comply with regulations. WHAT IS THIRD-PARTY AND SUPPLY CHAIN RISK? In the […]
Navigating the Risks and Rewards of Cloud Transformation
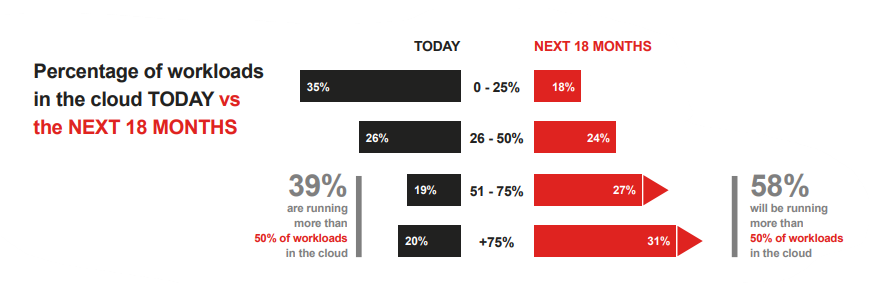
Cloud computing has changed the way businesses work forever. In its infancy, cloud computing offered little more than pay-as-you-go virtualisation, where compute resources were effectively rented from a provider for the duration needed and businesses were billed accordingly. The flexible scalability that the cloud offered meant that soon enough every organisation in the world had […]
How Digital Transformation is Reshaping Data Security
As a company becomes more digital – so does the need to implement more security around its data. Implementing advanced cyber security solutions and data management systems and ensuring compliance with data protection regulations may be the only way to effectively safeguard against emerging threats to data and the new vulnerabilities created by our increasingly […]
The AI-volution: Redefining Data Security and Privacy
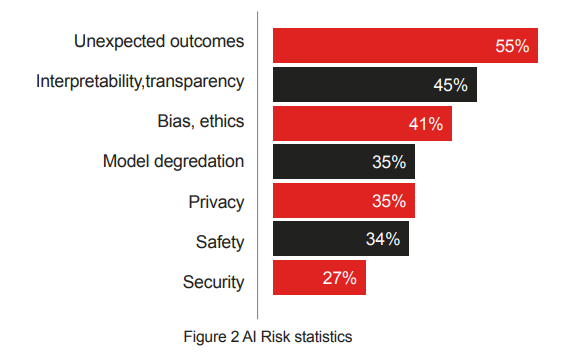
Artificial Intelligence (AI) has dominated the headlines in recent times, as governments and businesses the world over grapple with how to adopt and benefit from this evolving technology. It has been predicted that the adoption of AI and the efficiencies it delivers will allow world GDP to potentially double or even triple in size by […]